Promoting your website involves a multi-faceted approach that includes optimizing for search engines, leveraging social media, utilizing content marketing, and engaging in various digital marketing strategies. Here are some effective methods
Author: adminstud
How to Stay Motivated as a Student in a Tough Economy
Learn practical ways students can stay motivated, focused, and hopeful even in a tough economy and uncertain future.
Best Free Online Resources Every Student Should Know
Discover the best free online resources every student should know for learning, skills, productivity, and career growth.
How to Balance School, Skills Learning, and Personal Life
Learn practical ways students can balance school, skills learning, and personal life without stress or burnout.
Top Mistakes Students Make When Choosing a Career
Discover the top mistakes students make when choosing a career and learn how to avoid confusion, regret, and poor career decisions.
Skills vs Degree: What Matters More in 2026?
In 2026, do skills matter more than a degree? Learn what employers really want and how students can stay competitive in the future job market.
How to Discover Your Career Path as a Student (Even If You’re Confused)
Confused about your future? Learn how students can discover their career path step by step, even without clarity or experience.
What Is Student Vocation and Why Every Student Needs One
Discover what student vocation means, why it is important, and how students can find clarity, purpose, and career direction early.
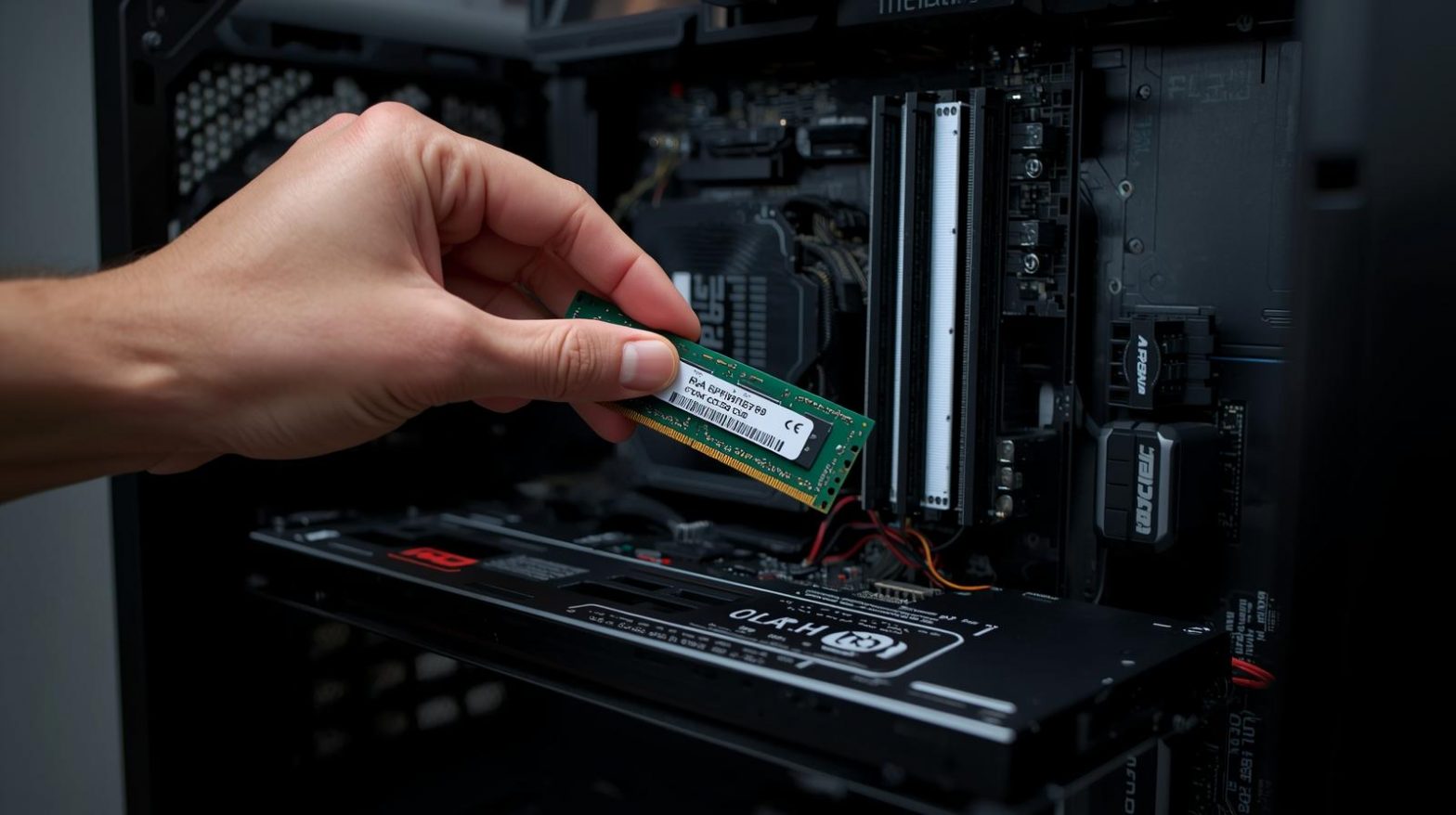
How to Safely Upgrade Your RAM for Better Performance
Upgrading your RAM (Random Access Memory) is one of the easiest and most affordable ways to improve your PC’s speed and multitasking performance — but it must be done safely and correctly.
Needing to know the official objectives of cyber security
The official objectives of cybersecurity are generally summarized by the CIA Triad, which stands for Confidentiality, Integrity, and Availability. These three core principles form the foundation of all cybersecurity strategies, policies, and frameworks worldwide.